Securing Your Business Against Cyber-Attacks And Data Breaches
Symantec Upgrade Promotion
Upgrade to Bitdefender, the best endpoint protection solution as ranked by AV Comparatives.
Contact us now for your special Symantec upgrade price!
Managed Compliance Service
Automate manual tasks with Secureframe’s AI-powered capabilities to efficiently manage security, risk, and compliance, saving you time so you can focus on your business and grow revenue.
Supports 50 over frameworks including ISO 27001, SOC 2 and PCI-DSS.

Regional Distributor
Stellar Cyber is revolutionising Security Operations with its Multi-Layer AI automation driven NG-SIEM, NDR and Open XDR platform.

Singapore Country Partner (exclusive Distributor)
BitCyber is proud and honoured to be appointed Bitdefender’s Singapore Country Partner. As the exclusive distributor, we will be building up Bitdefender’s brand and recruiting the best cybersecurity solution providers to secure your business.
Built For Resilience
Introducing Bitdefender XDR
Bitdefender’s industry leading Endpoint Detection and Response (EDR) capabilities have been proven at MITRE ATT&CK’s Evaluations
The Forrester Wave: Enterprise Detection & Response, Q1 2020
“Bitdefender is the biggest EDR vendor you haven’t considered but should have.”
Source: Bitdefender
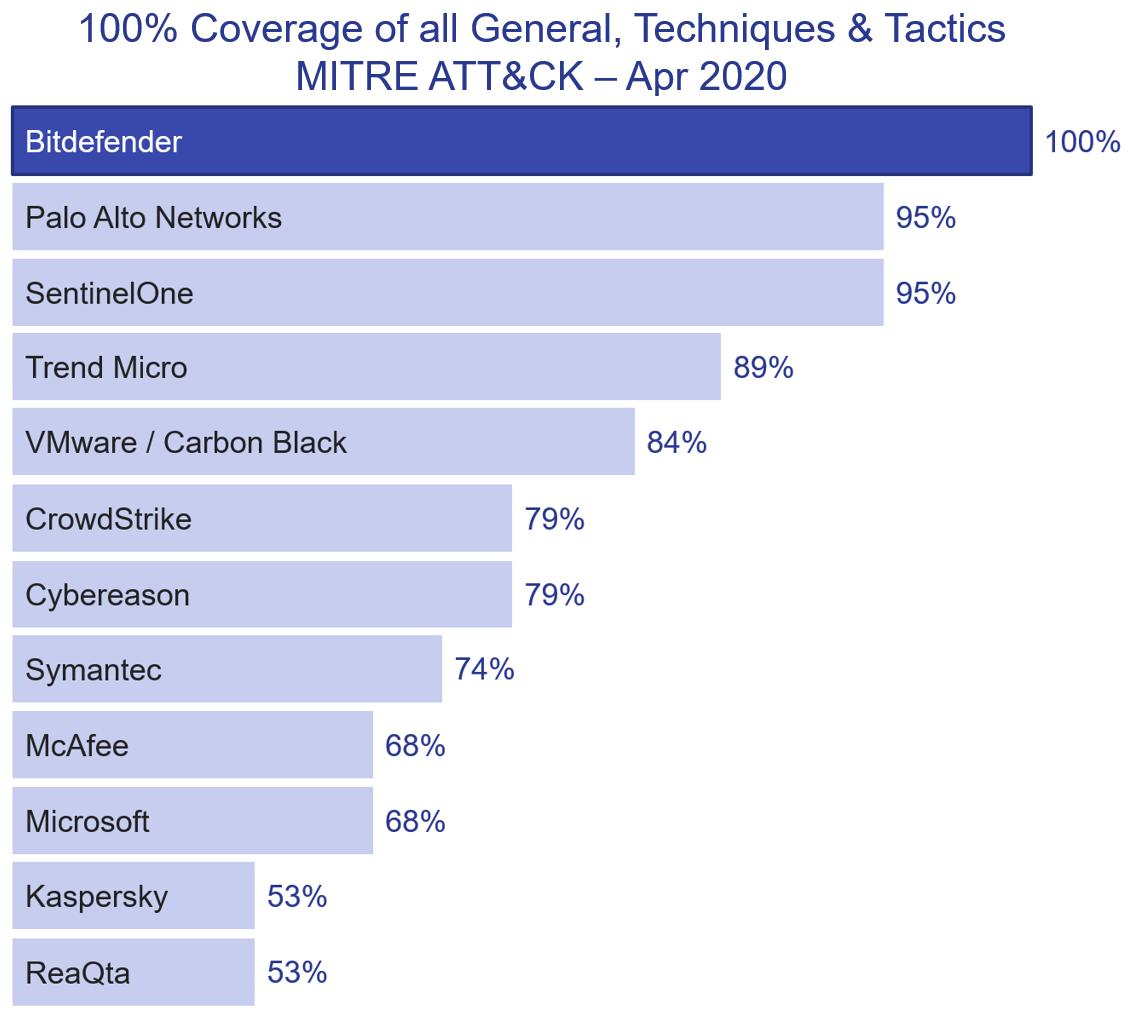
100% Coverage of Attack Kill Chain - MITRE ATT&CK Apr 2020
Bitdefender reaches 100% coverage after completing all 19 attack chain steps defined in the MITRE ATT&CK round 2 evaluation of APT29, Apr 2020.
Source: Bitdefender
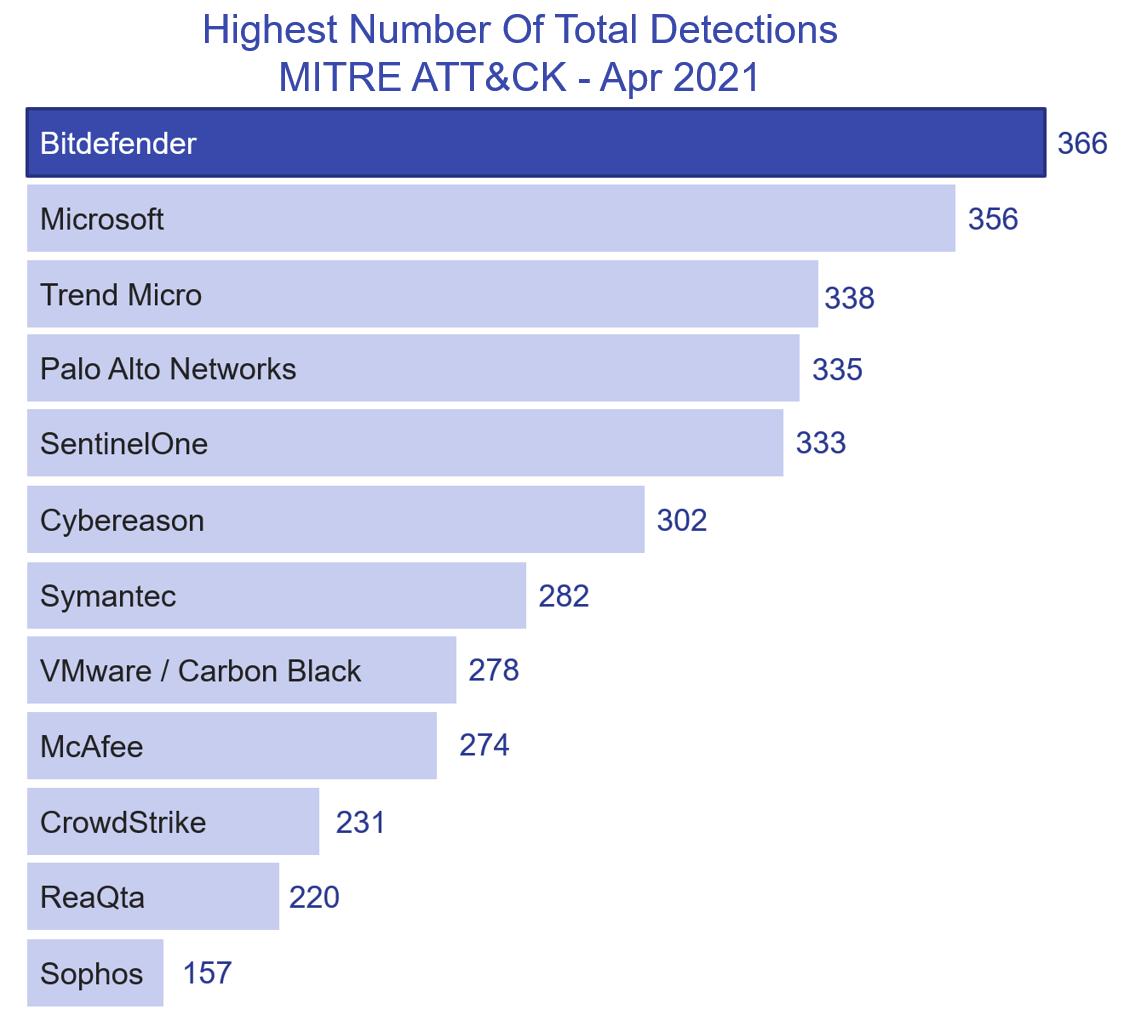
Highest Number of Total Detections - MITRE ATT&CK Apr 2021
The Detection Count represents the sum of detections of all types, including raw telemetry (like Process Starts or File Create) and analytic detections (like General Detection, Tactics or Attack Techniques).
Source: Bitdefender
Regional Distributor
BitCyber is honoured to be appointed by iboss Inc as their regional distributor. iboss is purpose built for Zero Trust to protect organizations from breaches and data loss.
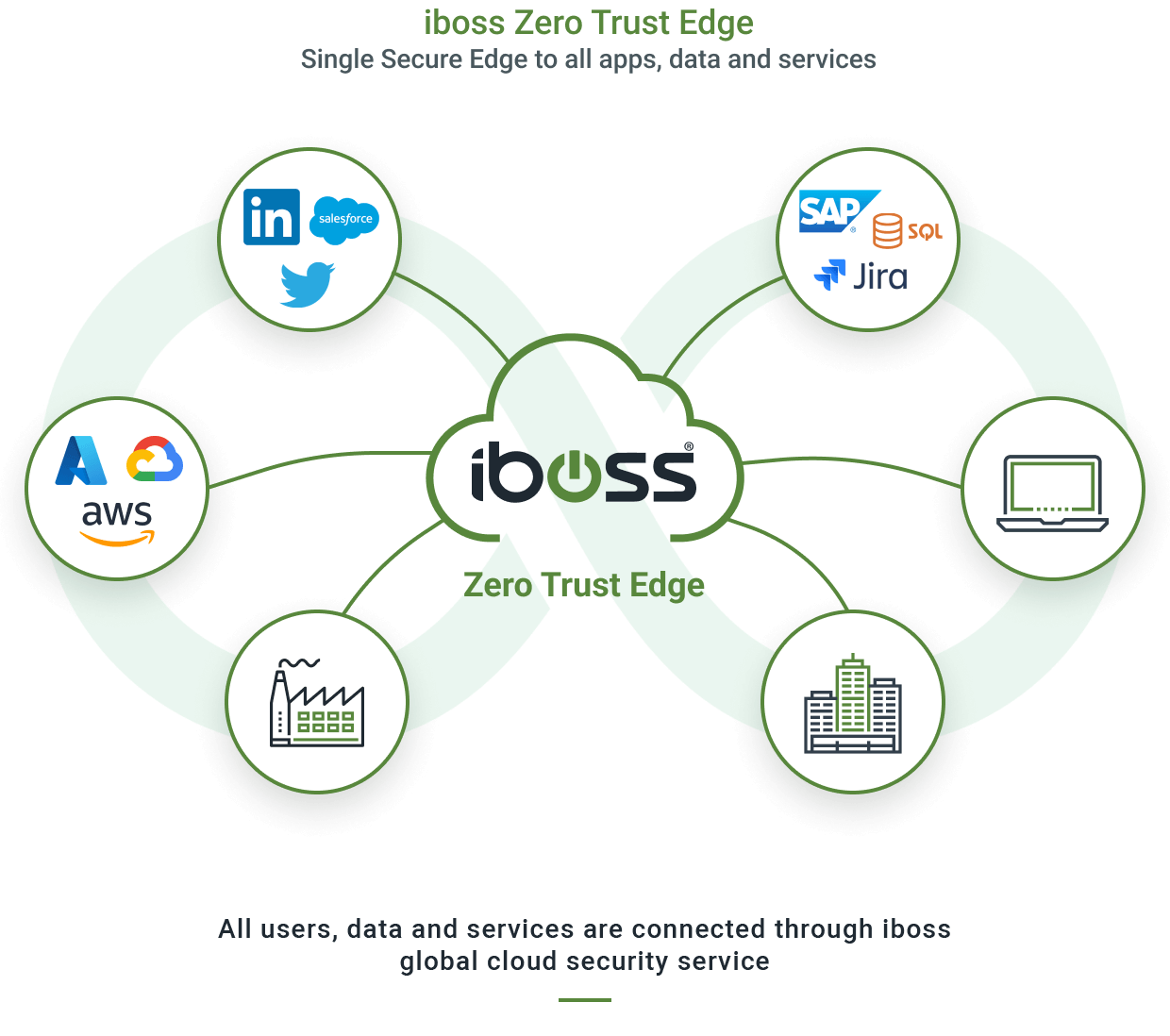
Zero Trust Edge SSE
Regional Distributor
Building Cyber Resilience with Continuous Threat Exposure Management (CTEM)
- What and why do we have Continuous Threat Exposure Management (CTEM)?
- Understand the CTEM 5 step journey.
- How can CISOs leverage AI technology in the CTEM journey?
Join this informative webinar to learn how Ridge Security’s AI-powered exposure management solution helps you reduce cyber risks and build a cyber resilience environment.
Regional Distributor
BitCyber is honoured to be appointed by Invisiron as their regional distributor. Invisiron is the leading autonomous threat protection solution.
Invisible Stealth Mode

Ultra Fast In-Line Packet Processing Speed

Autonomous Threat Prevention
Regional Distributor
BitCyber is honoured to be appointed by Virsec as their regional distributor. Virsec is the leading runtime application aware server workload protection solution.
Complete Runtime Visibility
Application Awareness
Comprehensive Protection

Singapore Distributor
BitCyber is honoured to be appointed by Falaina as their distributor for Singapore. Falaina is a comprehensive Identity and Access Management solution to meet today’s modern identity security needs.




Regional Distributor
BitCyber is honoured to be appointed by Infosec Ventures as their regional distributor in Singapore and the Asia region for their portfolio of innovative cybersecurity products.

The easiest uplift in cyber security overnight!


Security Risk Monitor is a SaaS platform that equips you with the ability to automatically and continuously IDENTIFY, MAP, SCAN, ASSESS & GRADE the risk portfolio of all your assets, vendor and acquisitions from the PERSPECTIVE OF A HACKER but COMPLETELY NON-INTRUSIVE